TL;DR
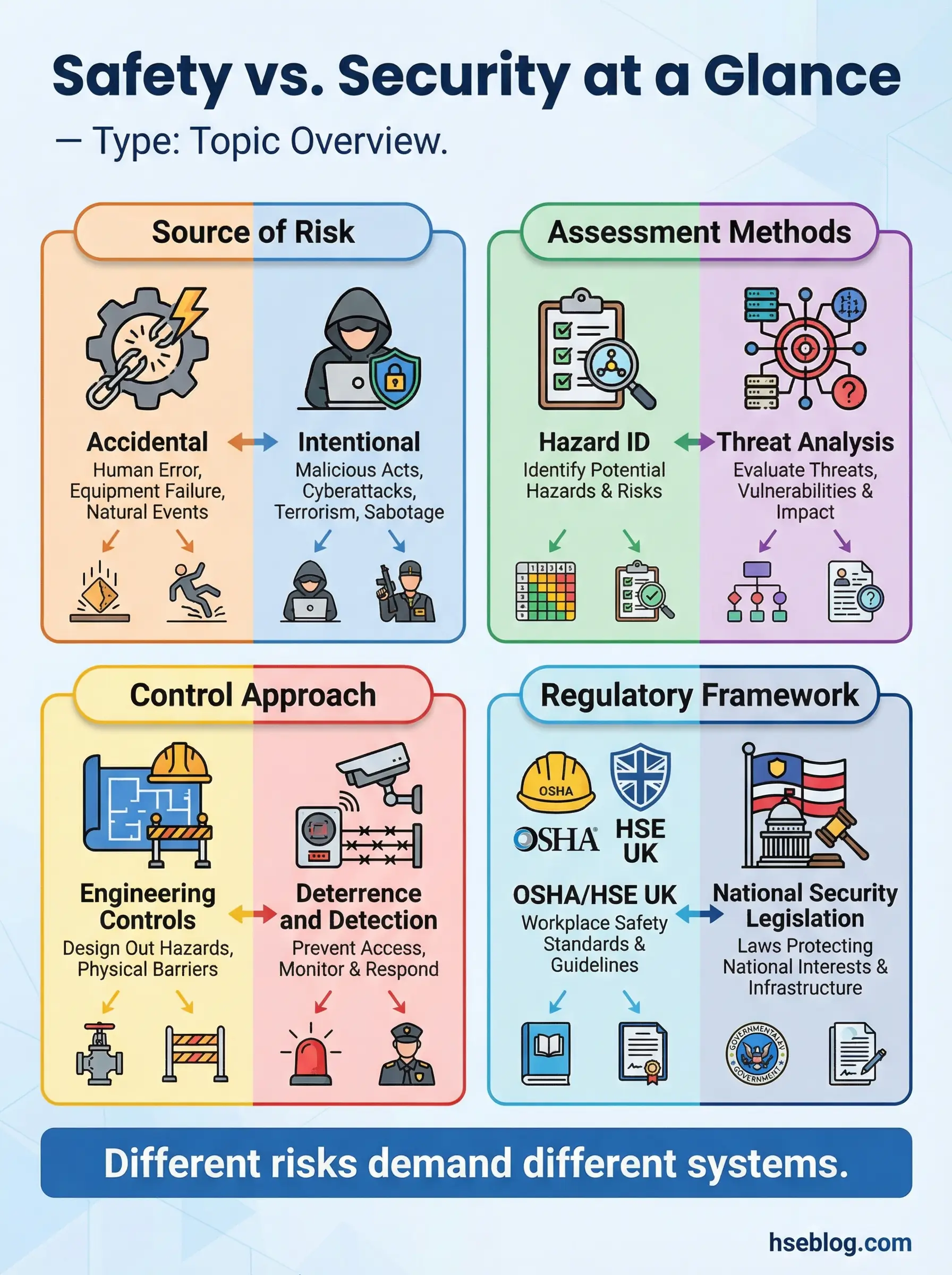
- Safety protects against accidental harm; security protects against intentional threats like theft, sabotage, or violence.
- Hazards drive safety programs; threats and vulnerabilities drive security programs.
- Both require risk assessment, but the source of danger — accidental vs. deliberate — changes every control measure.
- Merging safety and security functions creates blind spots that leave workers exposed on both fronts.
- Understanding the 10 key differences helps organizations allocate resources, assign roles, and close protection gaps.
I was auditing a logistics hub in the Middle East when the facility manager walked me through their “safety and security program” — a single binder with fire evacuation maps stapled next to visitor access logs and CCTV maintenance records. He used the terms interchangeably throughout the walkthrough. Thirty minutes into the audit, I found an unmanned loading dock where any vehicle could reverse in without identification checks, directly adjacent to a chemical storage area that lacked secondary containment. Two completely different failures — one a security gap, one a safety gap — both sitting in the same blind spot because nobody had separated them clearly enough to manage either one properly.
That experience captures a problem I see across industries. Organizations that blur the line between safety and security almost always under-resource one or the other. The difference between safety and security is not academic — it determines how you structure teams, allocate budgets, conduct risk assessments, and respond to incidents. This article breaks down 10 major differences that every HSE professional, site manager, and operations leader needs to understand, with field context drawn from petrochemical facilities, construction projects, and multinational operations.
What Is Safety and What Is Security? Core Definitions
Before comparing the two, each concept needs a clear operational definition — not a dictionary entry, but a working understanding that holds up on a job site.
Safety refers to the condition of being protected from unintentional harm arising from hazards — physical, chemical, biological, ergonomic, or environmental. A safety program identifies hazards, evaluates the risk they pose, and implements controls to prevent accidental injury, illness, or property damage. ISO 45001 frames this as eliminating hazards and minimizing occupational health and safety risks through systematic management.
Security refers to the condition of being protected from intentional acts — unauthorized access, theft, sabotage, workplace violence, terrorism, cyber intrusion, or espionage. A security program identifies threats, assesses vulnerabilities, and implements measures to deter, detect, delay, and respond to deliberate harmful acts.
The critical dividing line is intent. Safety addresses things that can go wrong accidentally. Security addresses things that someone makes go wrong deliberately. That single distinction reshapes every downstream decision — from risk assessment methodology to the qualifications of the people managing each function.
ISO 45001:2018 defines occupational health and safety as “conditions and factors that affect, or could affect, the health and safety of workers.” Security threats, while acknowledged as workplace risks, fall under separate governance frameworks in most jurisdictions.
The 10 Major Differences Between Safety and Security
Difference 1: Source of Risk — Accidental vs. Intentional
This is the foundational difference that drives all the others. Safety deals with hazards — conditions or situations with the potential to cause unintentional harm. A wet floor, an unguarded machine, a toxic vapor release. These are not targeted at anyone. They exist because of process conditions, equipment states, or environmental factors.
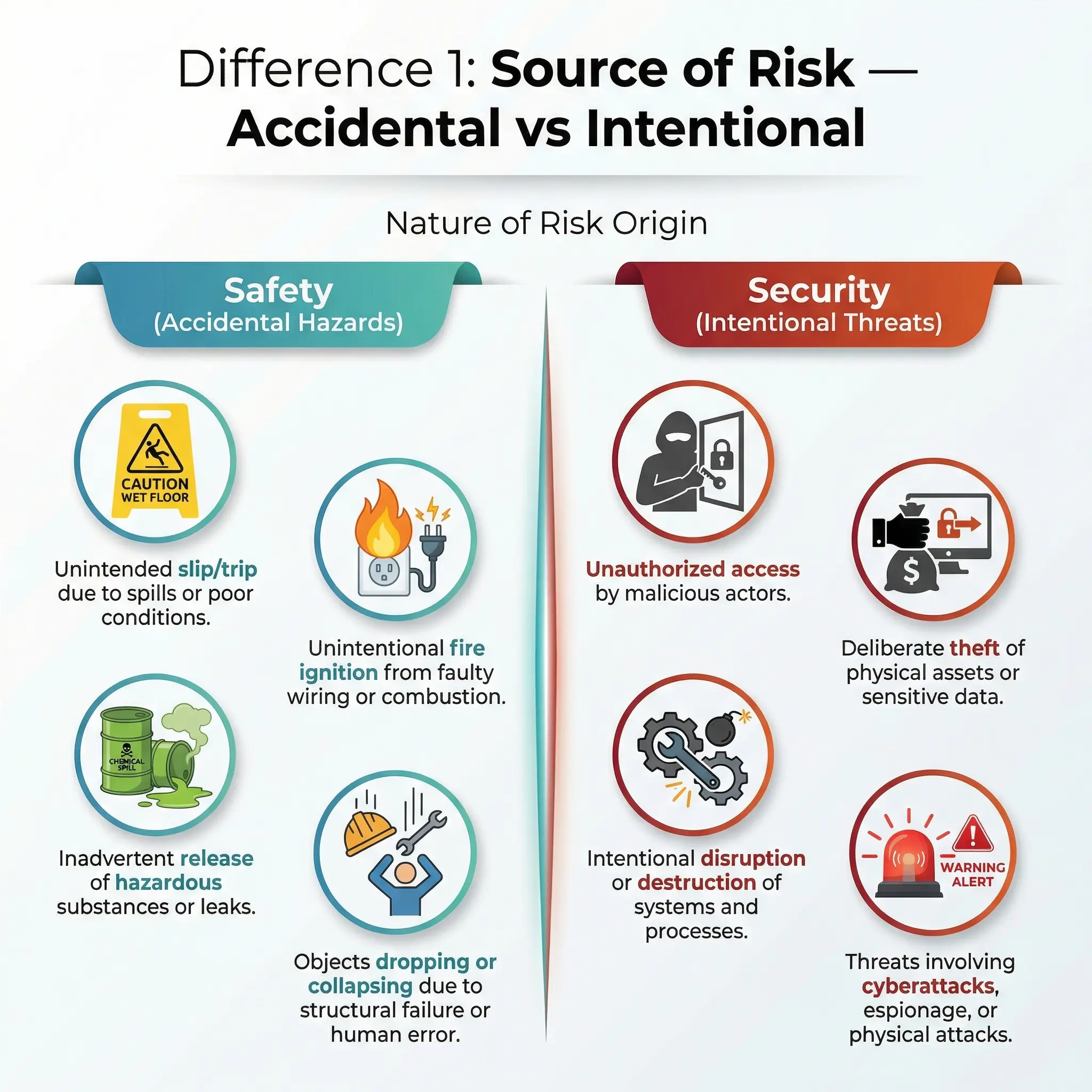
Security deals with threats — deliberate actions by people with hostile intent. An intruder entering a restricted area, a disgruntled employee sabotaging equipment, a cyberattack on a control system. The risk source is a conscious decision by a human actor.
During a shutdown at a petrochemical complex in the Gulf, I managed both types simultaneously. The safety side involved confined space entry permits, hot work controls, and crane lift plans. The security side involved controlling contractor access badges, preventing unauthorized photography of proprietary equipment, and monitoring for theft of copper wiring — which spiked during every shutdown because of the volume of temporary workers on site. Same plant, same week, completely different risk management approaches.
Difference 2: Risk Assessment Methodology
Safety and security both require structured risk assessment, but the tools and thinking differ fundamentally.
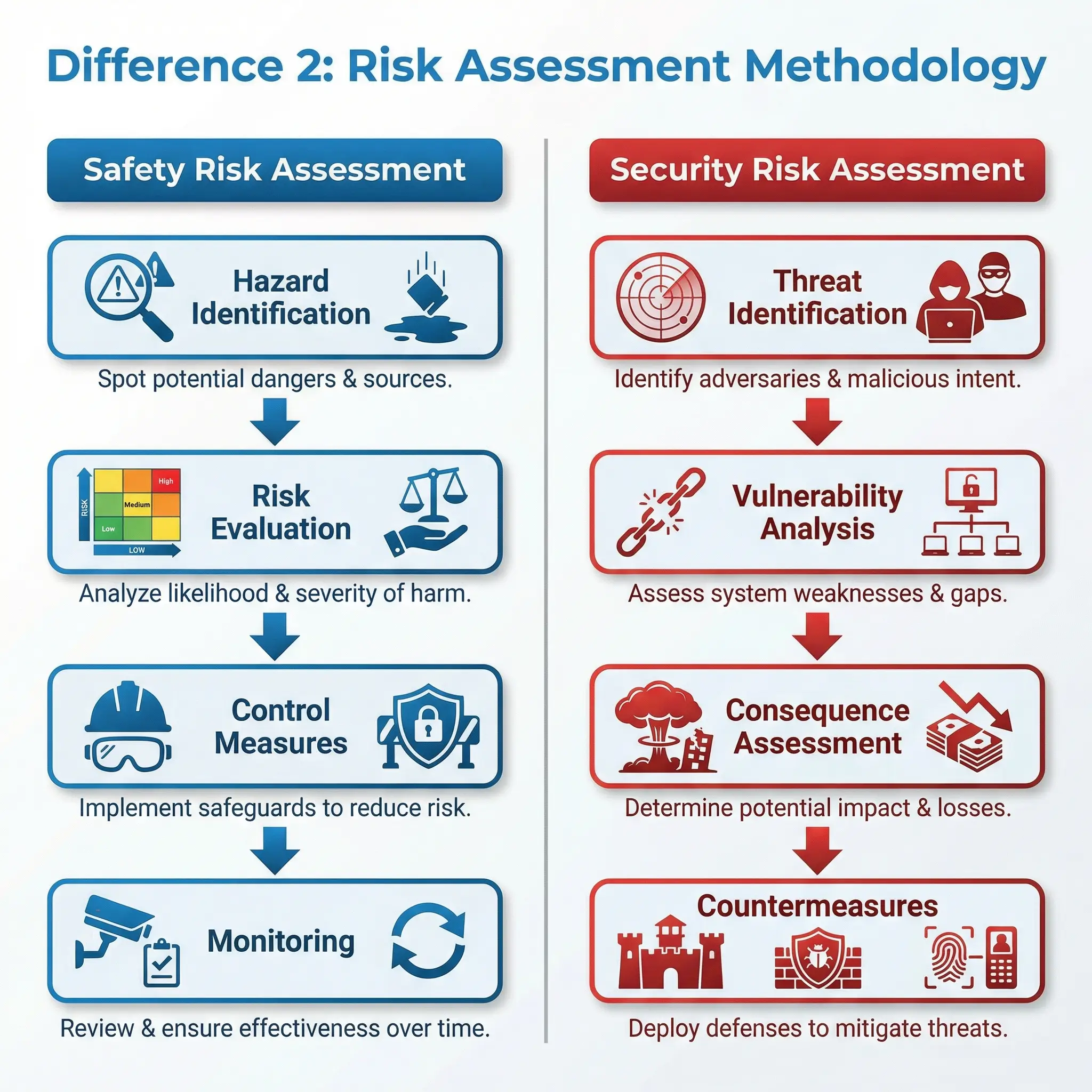
Safety risk assessments follow a hazard-based model familiar to any HSE professional:
- Hazard identification: Walk the site, review processes, examine task steps
- Risk evaluation: Assess likelihood and severity using a risk matrix
- Control hierarchy: Eliminate, substitute, engineer, administrate, PPE
- Monitoring: Inspect, audit, measure, review incident data
Security risk assessments follow a threat-vulnerability model:
- Threat identification: Who might act, what are their capabilities, what is their motivation
- Vulnerability assessment: Where are the weak points in physical barriers, access controls, information systems
- Consequence analysis: What is the impact if the threat exploits the vulnerability
- Countermeasures: Deter, detect, delay, respond
The safety approach assumes hazards are constant — gravity does not change its mind. The security approach assumes threats are adaptive — an adversary will change tactics when a vulnerability is closed.
Pro Tip: When conducting a site-wide risk assessment, run the safety and security assessments as parallel tracks with separate methodologies. Trying to force security threats into a standard safety risk matrix produces misleading risk scores because the likelihood component behaves differently when a thinking adversary is involved.
Difference 3: Regulatory and Legal Framework
Safety and security operate under different legal architectures in virtually every jurisdiction. Understanding which laws govern each function prevents compliance gaps.
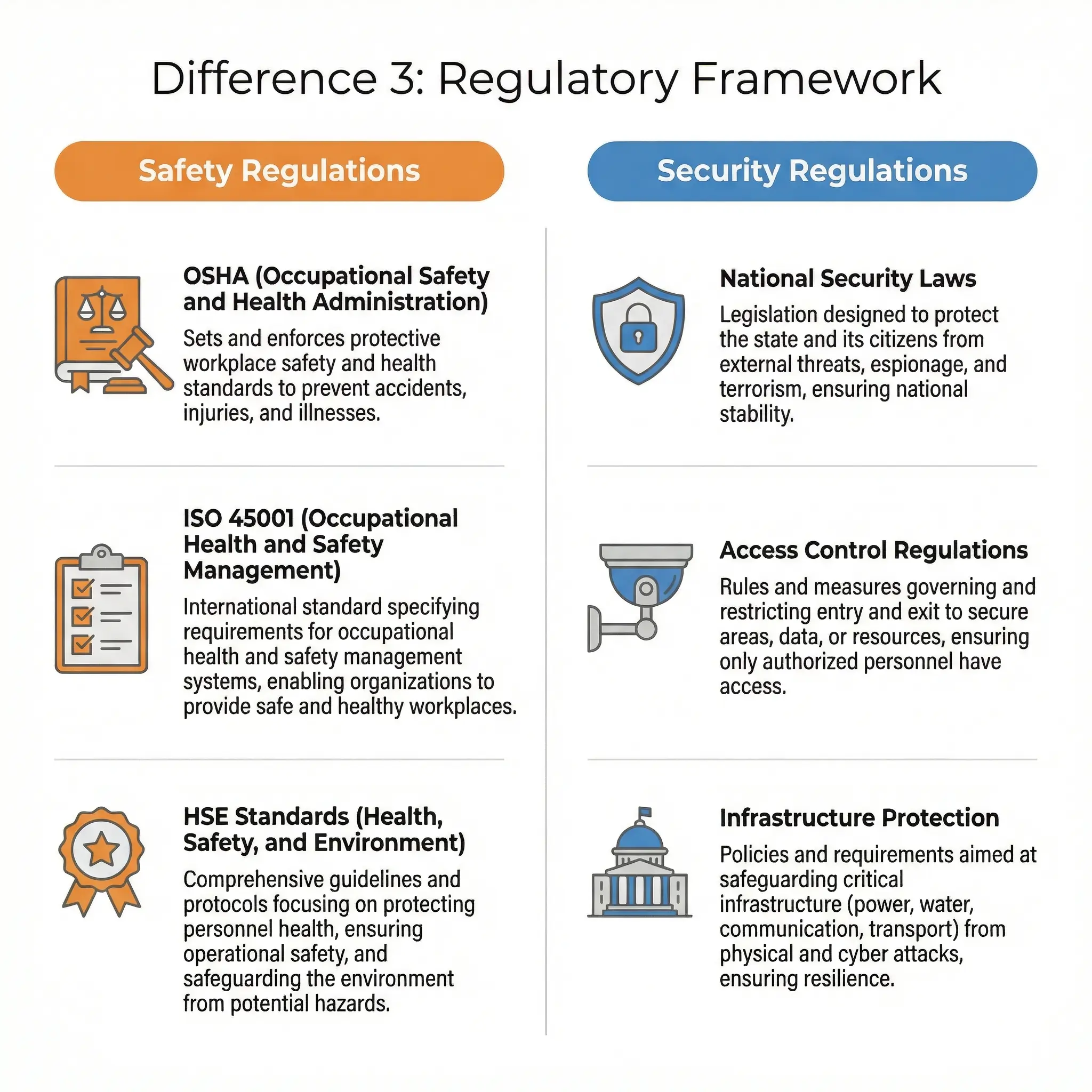
The regulatory landscape splits along predictable lines:
- Safety regulations come from occupational health and safety bodies — OSHA in the United States, HSE UK in Britain, EU Framework Directive 89/391/EEC across Europe. These mandate hazard identification, risk assessment, safe systems of work, training, and incident reporting.
- Security regulations come from national security agencies, law enforcement bodies, and sector-specific regulators — the Chemical Facility Anti-Terrorism Standards (CFATS) in the US, the Security Industry Authority (SIA) in the UK, ISPS Code for maritime facilities, and critical infrastructure protection directives.
I have seen facilities audited by safety inspectors and security regulators within the same month — and the two sets of findings never overlapped. The safety inspection focused on machine guarding, chemical storage, and emergency exits. The security audit focused on perimeter fencing, access control logs, and visitor management procedures. Both identified real risks. Neither covered the other’s territory.
Difference 4: Control Measures and Strategies
The hierarchy of controls — the backbone of every safety program — does not translate directly to security. Safety controls aim to prevent accidental contact with hazards. Security controls aim to deter, detect, delay, and respond to deliberate acts.

Here is how the control philosophy diverges in practice:
- Safety controls follow the hierarchy: elimination, substitution, engineering controls, administrative controls, PPE. The goal is to remove or reduce the hazard before it contacts the worker.
- Security controls follow the “4 Ds” model: deter (visible cameras, guards, signage), detect (alarms, sensors, surveillance), delay (barriers, locks, access layers), respond (security personnel, law enforcement, lockdown procedures). The goal is to make the target harder to attack and faster to defend.
A fire door serves both functions — it prevents fire spread (safety) and restricts unauthorized movement between zones (security). But the design criteria, testing standards, and management responsibilities are different for each function. I have seen fire doors propped open for convenience, which simultaneously violated the fire safety plan and the zone access control plan. Two violations, two regulatory citations, one propped-open door.
Pro Tip: Audit your control measures for dual-function elements like fire doors, emergency exits, lighting, and perimeter barriers. These are where safety and security conflicts most often hide — because one function’s requirement can directly undermine the other.
Difference 5: Personnel Qualifications and Roles
The people managing safety and security carry different qualifications, different legal authorities, and different professional frameworks.
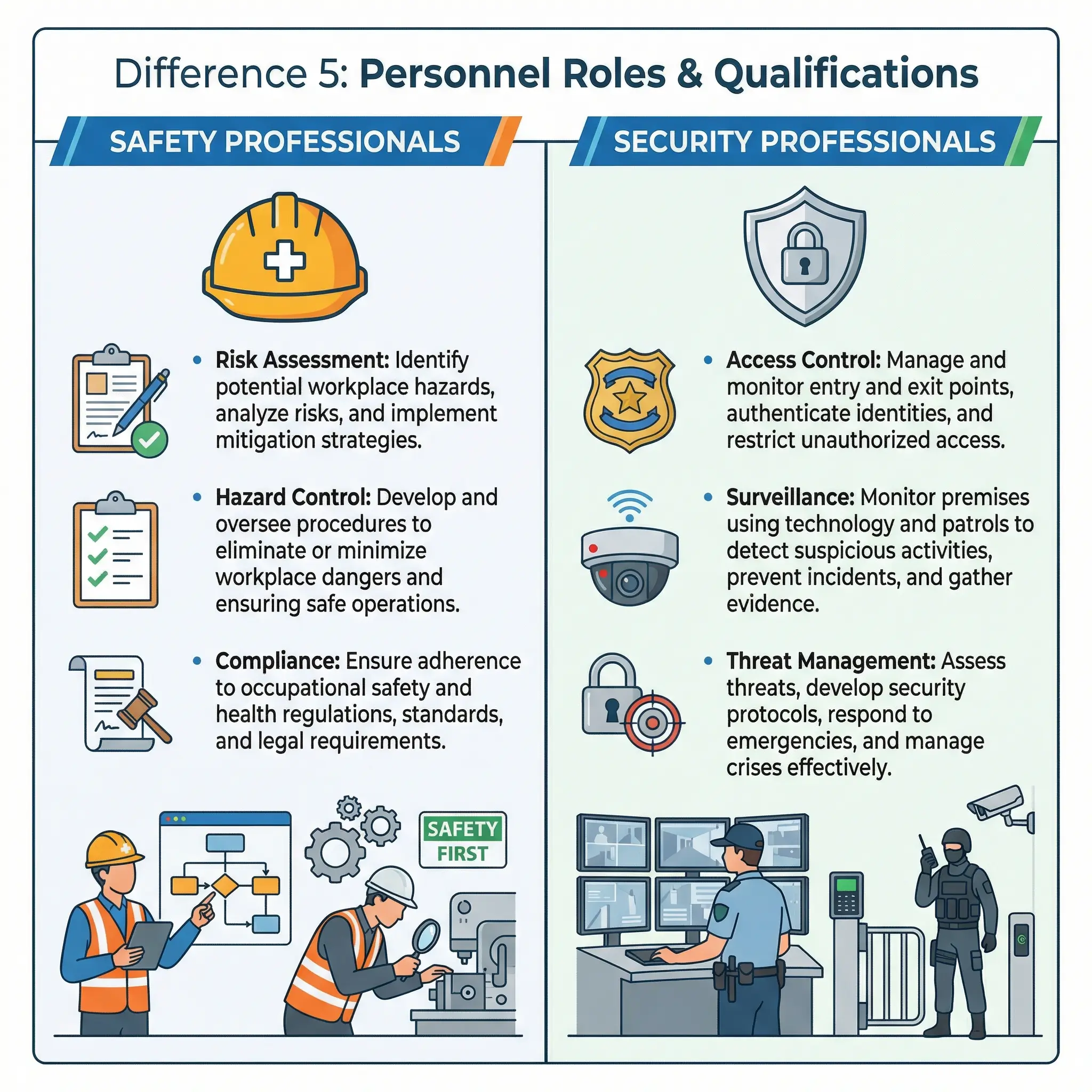
Personnel requirements reflect the fundamental difference in expertise:
- Safety professionals hold qualifications like NEBOSH, CSP (Certified Safety Professional), IOSH membership, or CIH (Certified Industrial Hygienist). Their authority derives from occupational health and safety legislation. They conduct risk assessments, develop safe systems of work, investigate incidents, and advise management on compliance.
- Security professionals hold qualifications like CPP (Certified Protection Professional) from ASIS International, PSP (Physical Security Professional), or national security licensing. Their authority may include powers of arrest, search, and detention depending on jurisdiction. They manage access control, conduct threat assessments, coordinate with law enforcement, and oversee surveillance systems.
On a large EPC project in Southeast Asia, our safety team and security team shared an office but operated under completely separate reporting lines. The safety manager reported to the project HSE director. The security manager reported to the client’s corporate security division. Both attended the daily site coordination meeting, but their briefings addressed different risks, different metrics, and different incident types. Mixing those reporting lines would have diluted accountability in both functions.
Difference 6: Incident Response and Investigation
When something goes wrong, safety incidents and security incidents follow different response protocols and investigation methodologies.
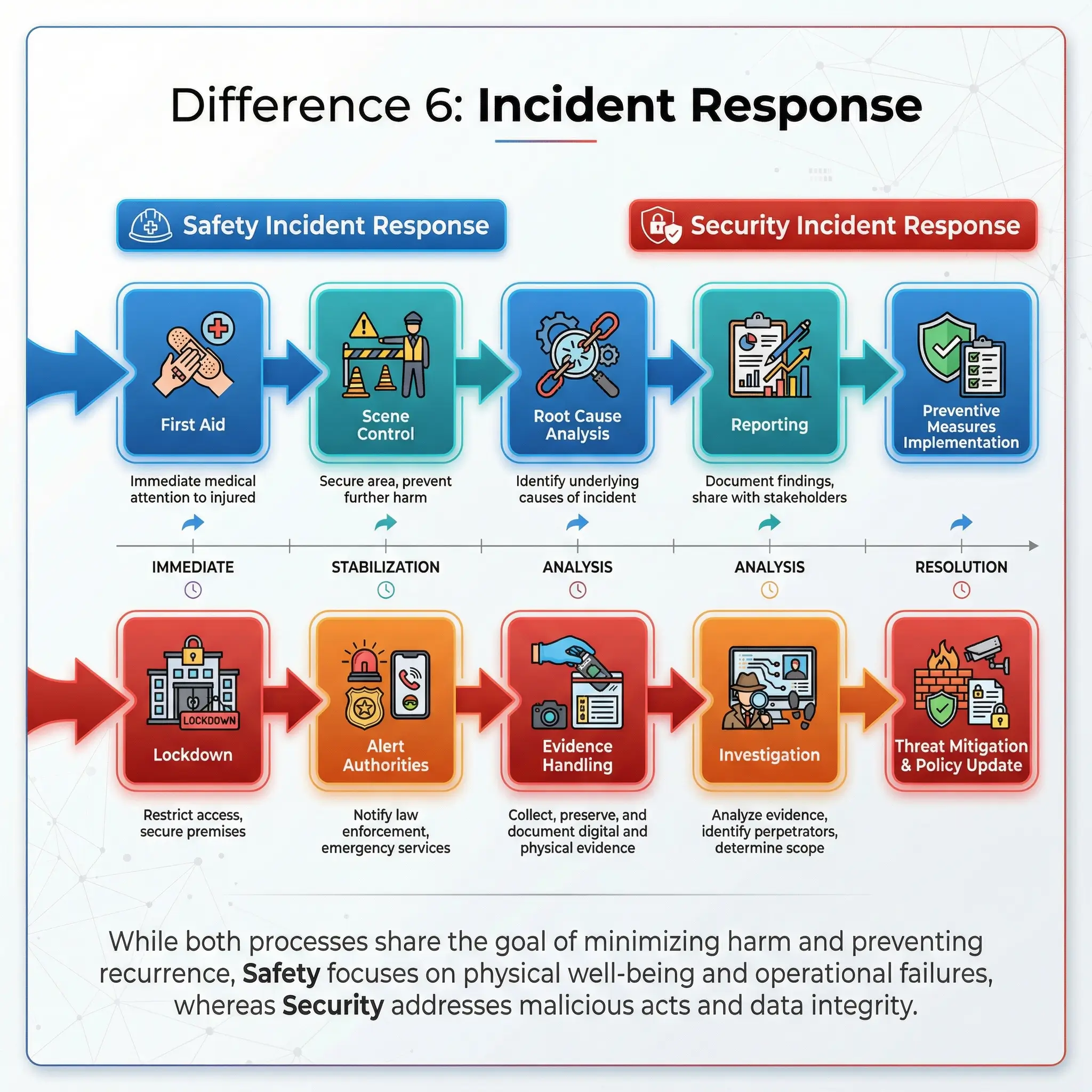
The response and investigation pathways diverge sharply:
- Safety incidents (injuries, near-misses, process upsets) trigger first aid or emergency medical response, scene preservation, root cause analysis using tools like the “5 Whys,” fishbone diagrams, or TapRooT, regulatory notification (OSHA recordables, RIDDOR in the UK), and corrective action plans reviewed through the safety management system.
- Security incidents (break-ins, threats, sabotage, workplace violence) trigger lockdown or evacuation, law enforcement notification, evidence preservation for criminal investigation, witness interviews conducted under chain-of-custody protocols, and insurance and legal notifications.
I investigated a warehouse fire at a distribution center in Northern Europe. The initial assumption was an electrical fault — a safety investigation. Forty-eight hours in, forensic analysis revealed accelerant traces near the point of origin. The investigation pivoted from safety to security — from accidental ignition to arson. The entire investigative team changed. The methodology changed. The legal framework changed. The reporting chain changed. Same fire, but once intent was established, every aspect of the response transformed.
Difference 7: Nature of Threats — Static vs. Adaptive
This difference changes how you maintain your programs over time. Safety hazards are fundamentally predictable. Gravity, chemical reactivity, electrical current, and thermal energy behave according to physical laws. A risk assessment conducted today remains valid until the process, equipment, or environment changes.
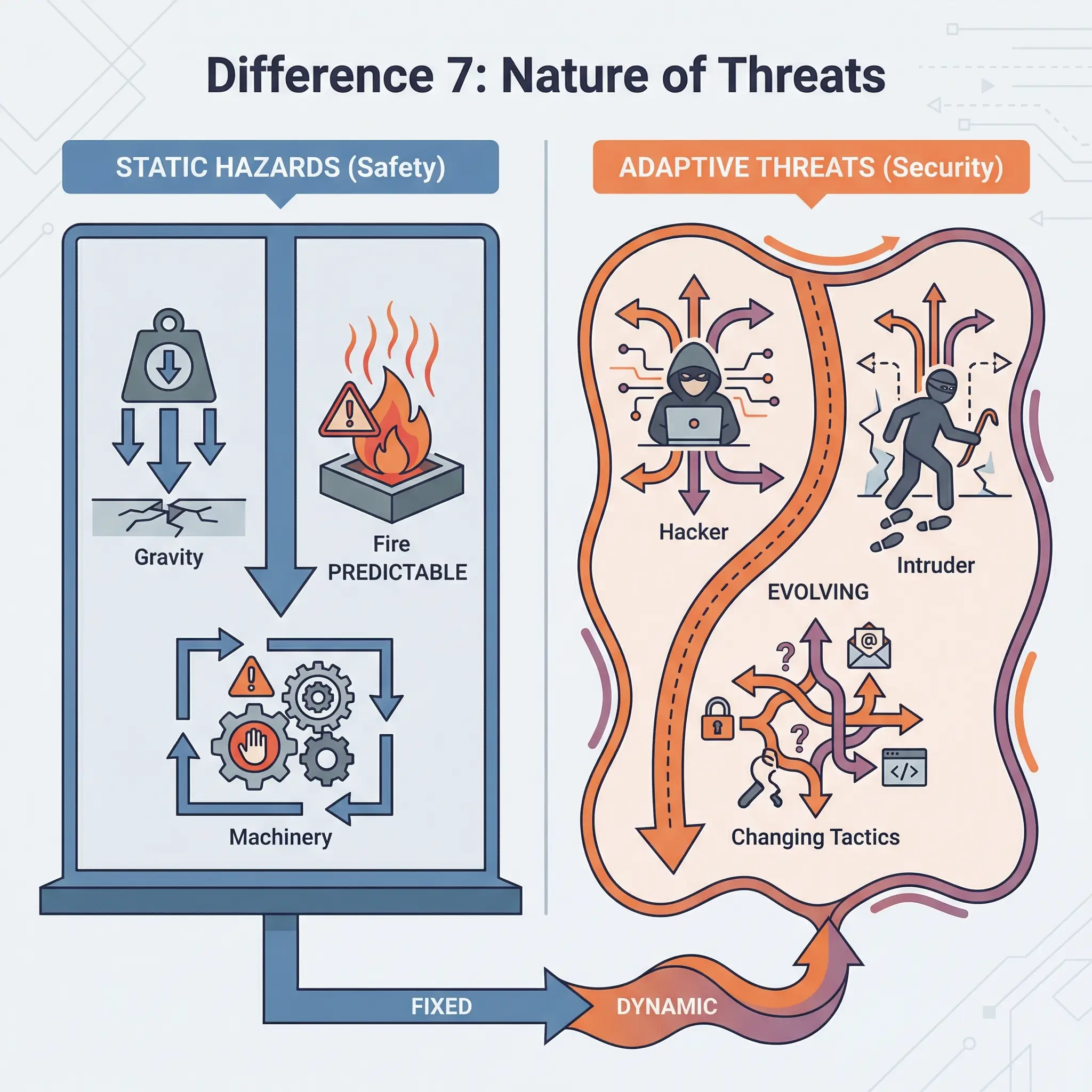
Security threats adapt. An adversary who finds one entrance blocked will try another. A theft method that fails once gets refined. A disgruntled employee who cannot access a system physically may attempt digital access. Security programs must assume that threats evolve in response to countermeasures.
This means security programs require continuous intelligence updates and vulnerability testing in ways that safety programs do not. A safety management system reviews risk assessments annually or after change. A security management system must treat its threat landscape as constantly shifting.
Pro Tip: If your organization only reviews security measures on the same annual cycle as safety risk assessments, you are almost certainly behind the threat curve. Security reviews should happen quarterly at minimum, and immediately after any personnel termination, organizational change, or external threat intelligence update.
Difference 8: Information Management and Confidentiality
Safety and security handle information transparency in opposite directions. Safety culture depends on open reporting, shared learning, and transparency. Near-miss reports, incident investigations, safety alerts — these are most effective when distributed widely. OSHA logs are public records. Safety data sheets must be accessible to every worker.
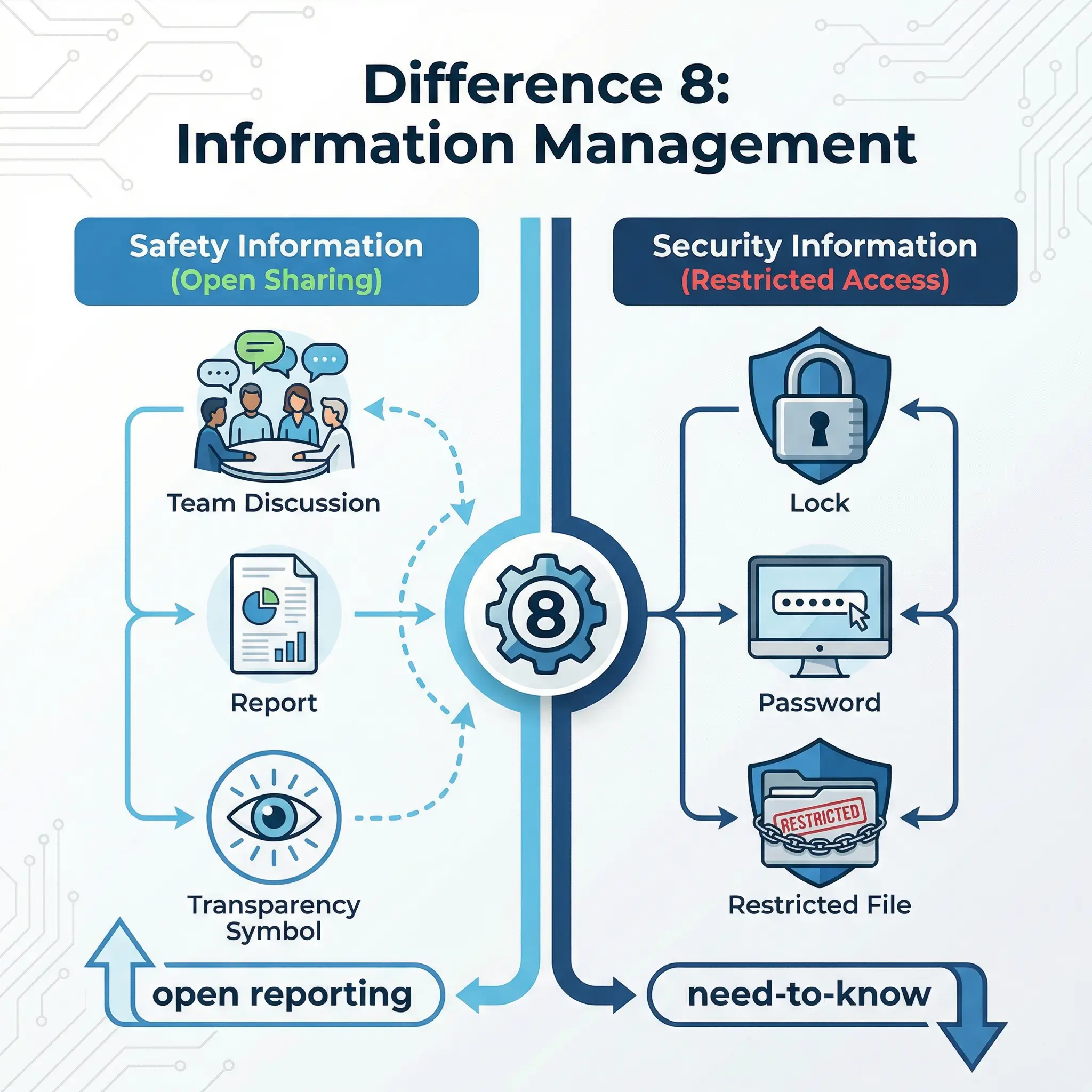
Security programs operate on a need-to-know basis. Vulnerability assessments, threat intelligence, access control configurations, surveillance coverage maps, and emergency response plans for security scenarios are restricted. Publishing your security gaps is the opposite of managing them.
This creates a practical tension I have navigated on multiple projects. During a management review at a mining operation in Western Australia, the safety team wanted to publish a lessons-learned bulletin about a perimeter breach that had allowed an unauthorized vehicle onto a blast zone. The security team objected — publishing the exact breach location and method would tell the next potential intruder exactly where and how to try. We compromised by publishing the safety lesson (unauthorized vehicles in blast zones) without the security detail (which perimeter section failed and why).
Difference 9: Culture and Behavioral Focus
Both safety and security depend on human behavior, but they shape behavior through different cultural mechanisms.

The cultural levers for each function work differently:
- Safety culture encourages reporting, peer observation, stop-work authority, open communication about hazards, learning from mistakes, and blame-free investigation. The goal is to make every worker a safety advocate who speaks up about risks.
- Security culture encourages vigilance, access discipline, information protection, challenge protocols (questioning unrecognized individuals), and reporting suspicious behavior. The goal is to make every worker a security-conscious gatekeeper who controls information and access.
These two cultures can coexist, but they sometimes pull in opposite directions. A strong safety culture says “leave all doors open for emergency egress.” A strong security culture says “keep all doors locked to prevent unauthorized access.” Resolving these tensions requires deliberate coordination — not simply defaulting to whichever function has more organizational power.
Difference 10: Measurement and Performance Indicators
How you measure success in safety versus security reflects everything discussed above. The metrics are fundamentally different because the risk sources are different.
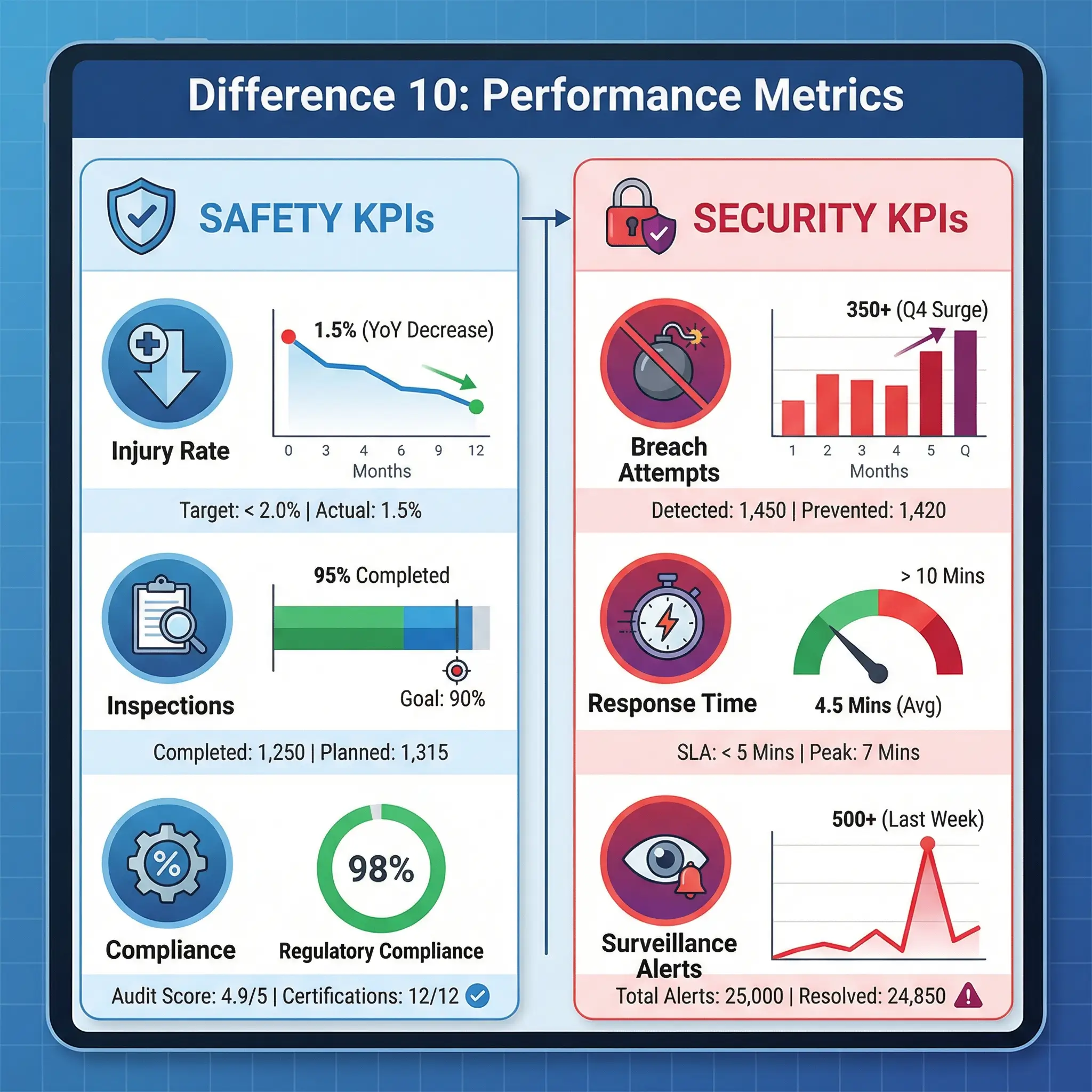
Performance measurement splits across distinct indicator sets:
- Safety KPIs include LTIR (Lost Time Injury Rate), TRIR (Total Recordable Incident Rate), near-miss reporting frequency, safety observation rates, training completion rates, inspection closure rates, and days since last recordable injury.
- Security KPIs include unauthorized access attempts detected, mean time to detect and respond to breaches, percentage of access points compliant with standards, security incident frequency, false alarm rates, guard tour completion rates, and penetration test results.
I have sat in management reviews where the safety dashboard showed green across the board — zero LTIs, high inspection rates, strong near-miss reporting. The security dashboard, presented thirty minutes later by a different team, showed three unauthorized access attempts in the same month, one successful perimeter breach, and a failed penetration test on the control room access system. The site was “safe” by every safety metric and dangerously exposed by every security metric. Without separate measurement systems, that security exposure would have been invisible.
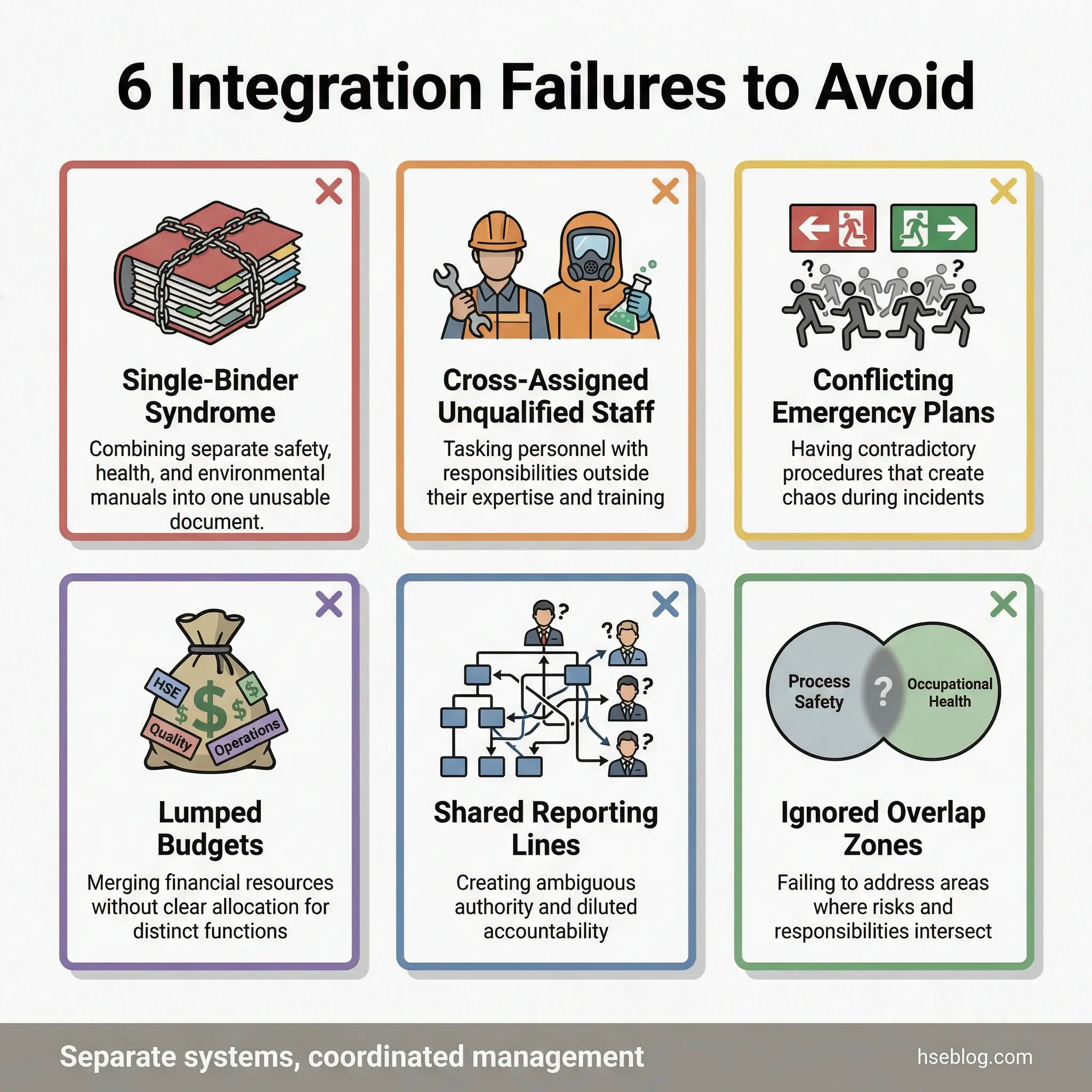
Common Mistakes: Where Organizations Get It Wrong
Even experienced operations mix up or merge these functions in ways that create real gaps. These mistakes appear repeatedly across industries and project types.
The most frequent errors I encounter during audits and management system reviews include:
- Single-binder syndrome: Combining safety and security into one policy document, one risk register, and one management review — which guarantees that one function gets less attention than the other
- Cross-assigning unqualified personnel: Asking the safety officer to manage access control, or asking the security manager to conduct hazard identification — both require specialized competence
- Emergency plan conflicts: Evacuation plans (safety) that conflict with lockdown plans (security), with no protocol for deciding which takes precedence during an active scenario
- Budget lumping: Allocating a single “safety and security” budget line, forcing the two functions to compete for the same resources instead of being resourced based on their distinct risk profiles
- Shared reporting lines: Both functions reporting to the same middle manager who lacks expertise in one or both disciplines, resulting in decisions made without adequate specialist input
- Ignoring the overlap zones: Failing to identify and formally manage the areas where safety and security controls interact — fire doors, emergency lighting, perimeter barriers, visitor management
Pro Tip: Conduct an annual “interface audit” specifically examining where safety and security controls overlap, conflict, or create gaps. This is the single most effective step I have seen organizations take to prevent the blind spots that neither function catches on its own.
Safety vs. Security: Side-by-Side Comparison Table
The following table distills all 10 differences into a quick-reference format for training sessions, toolbox talks, and management briefings.
| Aspect | Safety | Security |
|---|---|---|
| Source of Risk | Accidental hazards (physical, chemical, biological) | Intentional threats (theft, sabotage, violence) |
| Risk Assessment | Hazard-based: identify, evaluate, control | Threat-vulnerability model: threat, vulnerability, consequence |
| Regulatory Framework | OSHA, HSE UK, EU Directive 89/391, ISO 45001 | CFATS, SIA, ISPS Code, critical infrastructure laws |
| Control Philosophy | Hierarchy of controls (eliminate → PPE) | 4 Ds: deter, detect, delay, respond |
| Personnel | NEBOSH, CSP, CIH, IOSH-qualified professionals | CPP, PSP, SIA-licensed professionals |
| Incident Response | First aid, root cause analysis, OSHA/RIDDOR reports | Lockdown, law enforcement, criminal investigation |
| Threat Nature | Static and predictable (physical laws) | Adaptive and evolving (human adversary) |
| Information Handling | Open reporting, transparency, shared learning | Need-to-know, restricted access, classified data |
| Cultural Focus | Open communication, blame-free reporting, stop-work | Vigilance, access discipline, challenge protocols |
| Performance Metrics | LTIR, TRIR, near-miss rates, inspection scores | Breach detection rates, response times, penetration test results |
When Safety and Security Overlap — And How to Manage It
Despite the 10 differences, safety and security are not completely independent. Certain scenarios require coordinated response, and certain physical controls serve both functions simultaneously.
The most critical overlap areas demand formal coordination protocols:
- Active shooter / workplace violence: Requires simultaneous lockdown (security) and first aid / casualty evacuation (safety) — conflicting protocols must be pre-resolved, not improvised
- Bomb threat with hazmat presence: Security manages the threat assessment; safety manages the chemical exposure risk and evacuation routing away from hazardous areas
- Fire and arson: Initial response is identical (evacuate, suppress), but investigation diverges once intent is suspected — fire safety investigation becomes criminal arson investigation
- Sabotage of safety-critical equipment: A security incident that creates an immediate safety hazard — both functions must respond in parallel with clear command structure
I learned this lesson sharply during an emergency drill at an energy facility in Northern Africa. The drill simulated a disgruntled contractor who disabled a fire suppression system before starting a fire. The safety team activated the fire response plan. The security team activated the intruder response plan. Neither plan referenced the other. The drill exposed a twelve-minute gap where nobody had command authority over the combined scenario. That twelve-minute gap in a real event could cost lives. After the drill, we developed an integrated crisis command protocol that assigned clear authority when safety and security scenarios merge.
Best practice from IFC/World Bank EHS Guidelines: Organizations operating in high-risk environments should establish a unified crisis command structure that preserves the independence of safety and security functions during routine operations but integrates them under a single incident commander during combined scenarios.

Conclusion
The difference between safety and security is not a matter of terminology or organizational preference. It is a fundamental distinction in the source of risk, the method of assessment, the type of controls, the qualifications of the people managing each function, and the legal frameworks governing both. Treating them as one program guarantees that you will under-manage at least one of them — and the consequences of that gap show up as incidents that your existing system was never designed to prevent.
Every facility I have audited that successfully managed both functions did so by keeping them structurally separate but operationally coordinated. Separate risk assessments, separate qualified personnel, separate performance metrics, separate budgets — but shared crisis command protocols, joint interface audits, and regular cross-briefings. That model works because it respects the expertise each function demands while eliminating the blind spots that emerge when they operate in complete isolation.
The workers on your site deserve protection from both accidental hazards and intentional threats. No single program, no single binder, and no single professional can deliver both without compromise. Build both systems properly, staff them with qualified people, and make sure they talk to each other at the boundaries. That is not bureaucracy — that is the minimum standard of care for the people who show up to work every day trusting that someone has thought this through.

