TL;DR
- If a non-employee enters your premises, your duty of care extends to them — under OSHA’s General Duty Clause, HSWA Section 3, and ISO 45001, the obligation does not stop at your payroll.
- If a visitor’s destination involves operational hazards, a low-risk briefing is not enough — controls must scale to exposure (information-only → escort + PPE → permit-to-work integration).
- If your visitor sign-in is not connected to your evacuation plan, the log is administrative — not life-safety — sign-in data must be retrievable at the assembly point during a real emergency.
- If you collect visitor personal data, GDPR or CCPA timelines apply from the moment of collection — consent, purpose limitation, and retention discipline are not optional add-ons.
Visitor safety management is the systematic process of identifying, assessing, and controlling health and safety risks to non-employees on a workplace — including clients, contractors, delivery drivers, inspectors, and members of the public. It encompasses risk assessment, induction, emergency accountability, PPE, escort protocols, and visitor data protection, and arises from the employer’s legal duty of care.
There is a persistent belief in many organizations that visitor management lives at the front desk — that it is fundamentally about badges, sign-in sheets, and politely directing guests to the right meeting room. The legal record disagrees. The UK Health and Safety at Work etc. Act 1974, Section 3, places statutory weight on protecting non-employees alongside workers; OSHA’s General Duty Clause does not narrow its reach to people on payroll; and ISO 45001:2018 explicitly extends its scope to visitors and other relevant interested parties. Reception is the access point. The duty of care is a separate, heavier obligation — and the two are routinely confused in practice.
Treating visitor safety as a security task rather than an HSE discipline is one of the more common — and more expensive — misclassifications a business can make. When a delivery driver is injured at a loading bay, when a client tour passes through an active production zone without PPE, when an evacuation alarm sounds and nobody can confirm whether the contractor who signed in three hours ago has left or is still in the basement — these are not security failures. They are HSE failures with security symptoms. This article walks through what visitor safety management requires under the principal regulatory frameworks, how to build a tiered risk-based program that scales controls to exposure, and where the practitioner judgment calls actually land.

What Is Visitor Safety Management and Why Does It Matter?
Visitor safety management is the systematic identification, assessment, and control of health and safety risks to non-employees on a workplace. It is distinct from — and broader than — visitor management as the term is typically used in commercial software contexts, where the dominant focus is access control, badge issuance, and host notification. The two overlap; they are not the same thing.
The safety dimension is what carries legal and operational weight. A digital sign-in product is a useful tool. It is not, by itself, a program. The program addresses what happens to the visitor between sign-in and sign-out — every moment of exposure to the workplace’s recognized hazards.
“Visitor” itself is a category that flattens enormous variation. A client attending a boardroom meeting and a delivery driver backing into a logistics yard are both technically visitors, but the risk profile between them differs by an order of magnitude. The categories that matter for HSE purposes are these:
| Visitor Type | Typical Destination | Risk Profile | Standard Controls |
|---|---|---|---|
| Office guest / client | Reception, meeting rooms | Low | Sign-in, host escort, brief orientation |
| Delivery driver | Loading bays, yards | Moderate | High-vis PPE, designated routes, traffic management |
| Short-visit contractor | Operational areas | High | Full induction, permit-to-work, PPE, escort |
| Inspector / auditor | Variable, often high-risk | Moderate–High | Site-specific induction, PPE, escort |
| Public / open event attendee | Tour routes or designated zones | Low–Moderate | Briefing, controlled routes, supervision |
| Family member or guest | Office or designated areas | Low | Sign-in, escort, restricted area control |
The reason visitor safety is so often under-managed is structural: the responsibility falls between HSE, facilities, security, and HR, and tends to settle wherever there is least active ownership. Reception receives the visitors. Security issues the badges. HSE writes the policy. Facilities runs the building. HR handles the data. None of those four owns the integration. The most consistent finding when reviewing a visitor program with HSE peers is rarely that any single function is failing — it is that nobody is connecting the parts. Sign-in works. Badging works. Induction is delivered. Yet during a drill, when the visitor list is needed at the assembly point, it is on a clipboard locked in the empty reception area.
Legal Obligations and Duty of Care for Visitor Safety
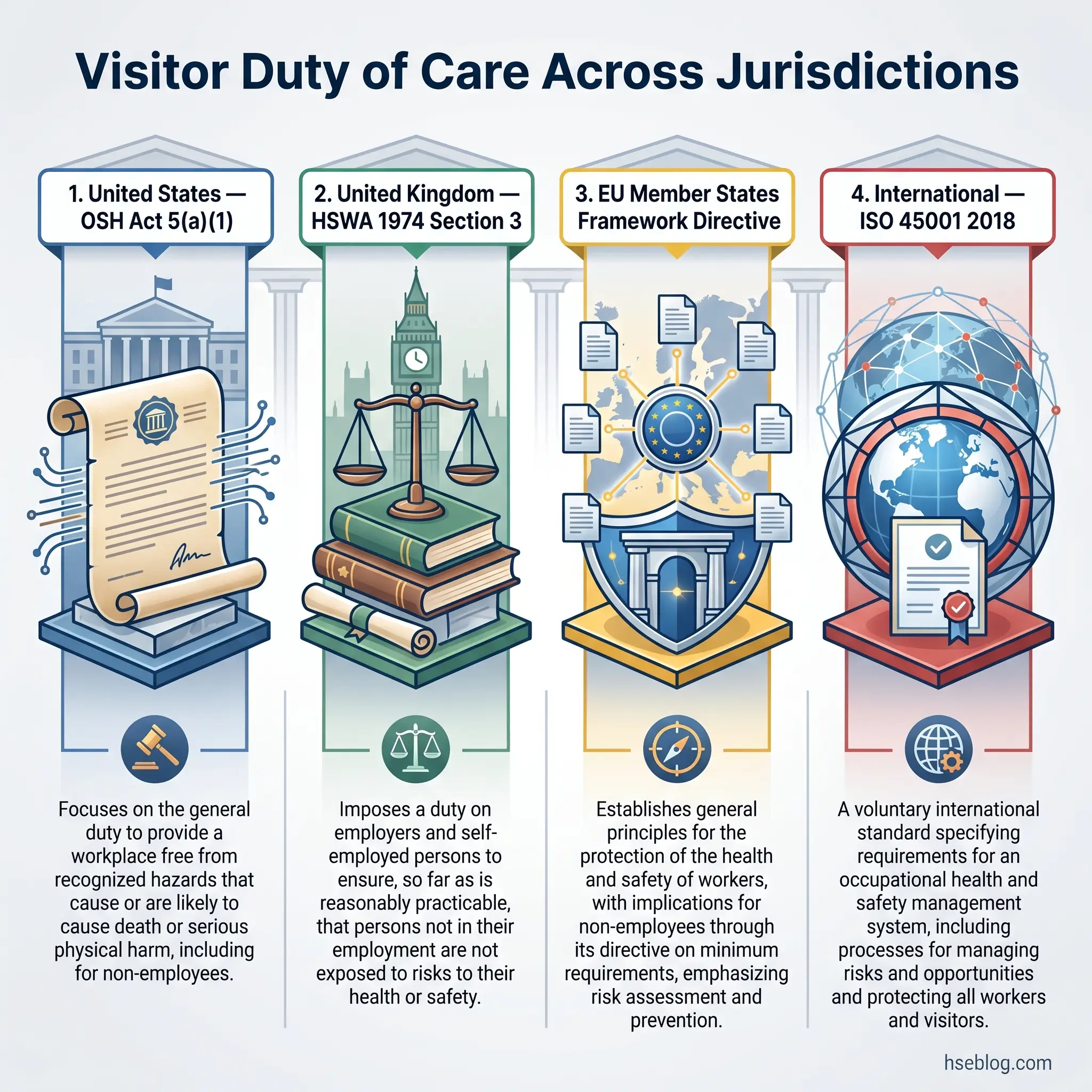
The duty of care owed to visitors is not a courtesy. It is a statutory or common-law obligation in every major jurisdiction, and the principal frameworks converge despite their different language. Three reference points dominate practice: the US OSH Act, the UK Health and Safety at Work etc. Act 1974, and ISO 45001:2018 — supplemented in EU/EEA territories by the General Data Protection Regulation when visitor personal data is involved.
In the United States, OSHA’s General Duty Clause, Section 5(a)(1) of the OSH Act, requires employers to provide a workplace free from recognized hazards likely to cause death or serious physical harm. The clause is worded around the employee relationship, but OSHA interprets it broadly, and specific standards have explicit non-employee reach. The Hazard Communication Standard, 29 CFR 1910.1200, protects “exposed persons” from hazardous chemical exposures — a phrase that takes in any non-employee who could foreseeably come into contact with the substance, whether they are a contractor, a delivery driver, or a visiting auditor.
In the United Kingdom, the duty is more explicit. Section 3 of the Health and Safety at Work etc. Act 1974 requires employers to ensure, so far as is reasonably practicable, that “persons not in their employment” are not exposed to risks to health and safety arising from the undertaking. The Management of Health and Safety at Work Regulations 1999 then require a “suitable and sufficient” risk assessment that covers all persons affected — visitors included. Layered on top, the Occupiers’ Liability Acts 1957 and 1984 create civil liability where premises occupiers fail to take reasonable steps to protect lawful visitors and, in qualified circumstances, even trespassers.
Internationally, ISO 45001:2018 is the most widely-recognized voluntary standard for occupational health and safety management systems. It explicitly aims to protect both workers and other interested parties — visitors named among them — from work-related accidents and diseases. Where the standard is implemented in earnest, visitor risk assessment is not an optional add-on; it is a core requirement under clause 6.1.2 (Hazard identification and assessment of risks).
| Jurisdiction | Primary Legislation | Duty Holder | Visitors Explicitly Named? |
|---|---|---|---|
| United States | OSH Act §5(a)(1); 29 CFR 1910.1200 (HazCom) | Employer | No — General Duty Clause applies broadly; HazCom protects “exposed persons” |
| United Kingdom | HSWA 1974 §3; MHSWR 1999; OLA 1957 / 1984 | Employer / Occupier | Yes — “persons not in his employment” |
| EU member states | National OHS laws transposing Framework Directive 89/391/EEC; GDPR for data | Employer / Data Controller | Variable; GDPR covers visitor personal data |
| International (voluntary) | ISO 45001:2018 | Organization | Yes — “workers and other interested parties” |
The misconception that catches organizations off guard during inspections is the assumption that OSHA standards apply only to employees. They do not. The General Duty Clause and substance-specific standards reach anyone exposed, and OSHA citations following non-employee injuries are well-documented in enforcement records. Where the legal exposure becomes uncomfortable is in the evidentiary trail — was the visitor briefed, did they sign for receipt, was the briefing appropriate to where they actually went? Inspectors and litigators ask exactly those questions.
Jurisdiction Note If you operate across borders, the practical rule is to apply the strictest applicable standard as your baseline. Where US, UK, EU, and ISO-aligned obligations all bear on the same site, harmonising at the highest threshold is simpler than maintaining tier-specific procedures and is better defensible during cross-jurisdiction audits.
The EU’s General Data Protection Regulation also enters the picture wherever visitor names, ID numbers, photos, host details, or vehicle plates are recorded. Cumulative GDPR fines have exceeded EUR 4.5 billion since 2018 (GDPR Enforcement Tracker, 2026), and visitor logs that are over-retained, over-collected, or unsecured are squarely within scope. The data dimension is not a separate compliance silo from visitor safety; it is a parallel obligation that runs alongside it.
How the Occupiers’ Liability Acts Apply to Workplace Visitors (UK)
In England and Wales, the occupiers’ liability framework is split across two statutes. The Occupiers’ Liability Act 1957 imposes a “common duty of care” on the occupier of premises to take such care as is reasonable in all the circumstances to ensure that lawful visitors are reasonably safe in using the premises for the purposes for which they are permitted to be there. The standard is reasonableness, not perfection — but the duty is owed as a baseline.
The 1984 Act extends a more limited, qualified duty to people who are not lawful visitors, including trespassers. The duty arises where the occupier is aware of a danger, has reasonable grounds to believe persons may be in its vicinity, and the risk is one against which it is reasonable to offer some protection. In practice, this means that occupiers cannot rely on dangerous physical conditions to “trap” intruders — nor can warnings alone always discharge the duty. A warning sign that does not enable a visitor to be reasonably safe in the circumstances is not enough on its own. Scotland operates under the Occupiers’ Liability (Scotland) Act 1960, which fuses the two duties into a single statutory standard.
Visitor Risk Assessment: Matching Controls to Exposure
The standard workplace risk assessment is built on an assumption that quietly fails when visitors arrive: the assumption that the person in the environment is familiar with it. Workers know where the alarms are, what each tone means, where assembly points sit, how to read site-specific signage, and what muscle-memory routes to take when something goes wrong. Visitors carry none of that. A risk assessment that is fit for employees may be entirely insufficient for the visitor exposed to the same hazard.
Three factors elevate visitor risk relative to the employee population: unfamiliarity with routes and exits, absence of task-specific training, and the lack of repeated drill exposure that builds reliable emergency response. Add language differences and visitors who arrive under time pressure, and the risk profile starts to look quite different from the assumption baked into the standard assessment.
The most useful operational response is a tiered classification of visitors by destination and exposure, with controls that scale accordingly:
| Visitor Tier | Areas Visited | Hazard Profile | Controls |
|---|---|---|---|
| Tier 1 — Low | Reception, conference rooms, office floors | General office hazards; egress routes only | Sign-in, host escort, brief verbal orientation or evacuation card |
| Tier 2 — Moderate | Warehouses, yards, semi-operational zones | Vehicle traffic, manual handling, falling objects | Documented induction, mandatory PPE, defined routes, host or escort |
| Tier 3 — High | Production lines, plant rooms, confined spaces, hot-work zones | Energy sources, atmospheric hazards, mobile equipment | Full safety induction, permit-to-work integration, full PPE, continuous escort by a competent person |
Tier classification is also dynamic. A visitor can begin a visit at Tier 1 (boardroom) and shift to Tier 2 or Tier 3 mid-visit (production tour). The risk assessment must anticipate the highest tier the visit could plausibly reach and equip the visitor accordingly — not retrospectively patch the gap when the host decides on a whim to detour through the production floor.
A consistent failure mode in published OSHA inspection findings and HSE UK case summaries is the application of a single, generic induction across every tier. The 20-minute briefing that suits a contractor entering a confined space is overwhelming for a boardroom visitor; the same 20 minutes is grossly insufficient for the contractor. Both errors increase exposure — one by inducing visitor disengagement, the other by leaving genuine hazards uncovered. Effective visitor risk assessment scales control to actual exposure, and revisits the assessment whenever the visit’s profile changes.

Visitor Safety Induction: Content, Delivery, and Verification
The induction is where the legal duty becomes operational. It is also where most visitor safety programs reveal their weak points — usually through over-engineering at the office tier and under-engineering at the operational tier.
The content of an induction has to be matched to where the visitor is actually going. For a Tier 1 office visit, a short verbal orientation and a simple evacuation card may discharge the duty. For Tier 2 and Tier 3 visits, the induction needs to cover the substance — site-specific hazards, alarm tones, evacuation routes from this destination, PPE requirements, restricted areas, incident reporting, and host responsibilities. Eight elements form the minimum content set:
- Site-specific rules and prohibited behaviors (no photography, no unauthorised entry to marked zones, no smoking or vaping)
- Emergency alarm tones and what each one means (fire, evacuation, shelter-in-place, all-clear)
- Evacuation routes from the visitor’s specific destination — not generic site routes
- Assembly point location and the route to reach it
- PPE requirements for the areas the visitor will enter, with correct fitting and inspection
- Restricted areas and the boundary signage that marks them
- Incident and near-miss reporting procedure and the host’s contact details
- Host or escort responsibilities — including the host’s reachability throughout the visit
Delivery method matters as much as content. A printed safety card, a video, a verbal briefing, and a digital induction all have legitimate uses, but they are not interchangeable. Verbal briefings allow questions and confirm comprehension; digital inductions provide auditable sign-off and consistent content across sites; video supports multilingual delivery; printed cards are useful as a take-with reference. The choice depends on visitor tier and on language and literacy considerations.
Language is one of the more under-addressed weak points. Where a workforce or visitor population includes non-native speakers, induction materials should be available in the relevant languages, and visual communication — pictograms, color-coded signs, demonstrated PPE fitting — should carry the weight that text cannot. Comprehension verification should follow: a quick question-back at the end of a verbal briefing, or a short knowledge confirmation in a digital induction.
Watch For The most fragile moment in the visitor process is the gap between sign-in at reception and the safety briefing — particularly when the briefing happens at a separate location with the host. If a visitor signs in at 09:02 and is briefed at 09:14, an alarm at 09:08 finds them in transit, with no knowledge of routes, alarms, or assembly points. Brief at sign-in, or escort the unbriefed visitor every step.
The verification step is what closes the loop. For Tier 1 and Tier 2 visits, an acknowledged sign-off — paper or digital — is the documentary evidence that induction was delivered. For Tier 3 visits, sign-off alone is insufficient: a competency check, however brief, is what demonstrates the induction was understood. Auditors and inspectors look for that distinction, and increasingly so do plaintiffs’ lawyers in occupier-liability proceedings.

Emergency Preparedness: Accounting for Visitors During Evacuations
Reviewing post-incident accounts of evacuations across published HSE guidance and OSHA emergency preparedness materials, a recurring pattern emerges: visitors are signed in but not yet briefed when an alarm sounds, and nobody can give them a credible answer about where to go. The accountability system fails before it starts.
OSHA’s emergency preparedness guidance is explicit on the point that visitors should be accounted for following an evacuation, and it identifies the host or warden system as the standard mechanism. The principle is that every visitor on the premises is logged at sign-in, that the log is accessible at the assembly area in real time, and that named personnel are responsible for confirming visitor presence at roll call. Where the log is paper-only and locked in reception, the principle fails on contact with reality.
The role of evacuation wardens carries particular weight for non-employees. Wardens are the ones who guide visitors who do not know the routes, who cannot interpret alarm tones, and who may panic in an unfamiliar space. The warden’s instruction is not just where to go — it is calm, audible, and authoritative direction that compensates for the visitor’s missing site knowledge. In multi-employer workplaces, the host’s role parallels the warden’s: the host is the visitor’s anchor throughout the visit and the person responsible for guiding them out.
Real-time accountability methods sit on a spectrum. A paper log at reception has the lowest fidelity — useful only if someone retrieves it before evacuating. A cloud-based VMS log accessible from a mobile device at the assembly point is the higher-fidelity option, allowing the warden to confirm visitor presence by name without leaving the assembly area. Whichever method is used, the test is the same: during a drill, can the visitor list be checked against bodies present, within the time window for the all-clear?
Visitors with disabilities, mobility limitations, or sensory impairments require advance planning. The duty does not relax because the person is on-site for thirty minutes. Pre-arrival communication with the host should establish whether evacuation assistance is needed, whether the chosen route accommodates the visitor’s needs, and whether a designated assistant is required. Drills should include visitors who happen to be present — drills that exclude visitors do not test the visitor accountability system.
The 2025 update from UK HSE on Workplace (Health, Safety and Welfare) Regulations 1992 guidance, focused on welfare facilities for visiting delivery drivers, signals a broader regulatory trajectory: visitor and non-employee accountability is moving from an implied duty toward an explicit one, with named populations attracting specific obligations. Organizations that have built visitor evacuation accountability into their drill programs are positioned for that shift; those that have not are likely to find themselves catching up under enforcement pressure.

What Should a Visitor Safety Policy Include?
Half of companies have experienced one to five on-site security incidents, according to the Envoy Workplace Report (2025) — a number that under-represents visitor-related risk because it counts incidents, not exposures. The number of times a visitor is on-site without proper accountability is necessarily larger than the number of times something goes wrong. A robust visitor safety policy is the governance framework that converts that exposure into managed risk.
The components of an auditable, implementable visitor safety policy are these:
- Scope and applicability — the visitor categories the policy covers, the premises and times of operation in scope, and any exclusions (e.g., contractors covered under separate contractor management procedures)
- Pre-visit requirements — pre-registration via host, host accountability for the visitor, pre-arrival safety information shared in advance for higher-tier visits
- Arrival procedures — sign-in, ID verification where required, badge issuance, safety briefing or induction matched to tier
- On-site rules — escort requirements, restricted area boundaries, PPE, photography or recording prohibitions, prohibited behaviors
- Departure procedures — sign-out, badge return, confirmation of off-site status before close-out
- Roles and responsibilities — reception, host employee, HSE team, security, evacuation wardens, with named functions rather than named individuals
- Data handling — collection purpose, consent capture, retention period, deletion mechanism, data subject rights under GDPR or CCPA
- Review and update — review frequency (annual minimum), trigger events (incidents, regulatory change, organizational change)
The most common policy failure I see in HSE practice is over-complexity. A policy that reads like a 20-page treatise is not implemented at the front desk; what is implemented is whatever the receptionist remembers, supplemented by informal workarounds that defeat the policy’s purpose. Effective policies are short enough to be followed and specific enough to be audited. If the receptionist cannot summarize the visitor policy in two minutes, the policy is not operational.
Audit Point Auditors typically test a visitor safety policy not by reading it but by walking it. They watch a real visitor arrive, observe whether sign-in matches the policy, ask the host what they were told to do, request the visitor list during a simulated alarm, and check whether the data retention period in the policy matches the data actually held in the VMS. Any of these can fail independently. All four routinely do.
The policy is the document. The procedures are how the document operates day-to-day. Policies that prescribe outcomes but do not name accountable functions tend to drift; policies that prescribe both, and that match the procedures employees actually run, hold up in audits and in litigation discovery.

Digital Visitor Management Systems: Safety Capabilities Beyond Check-In
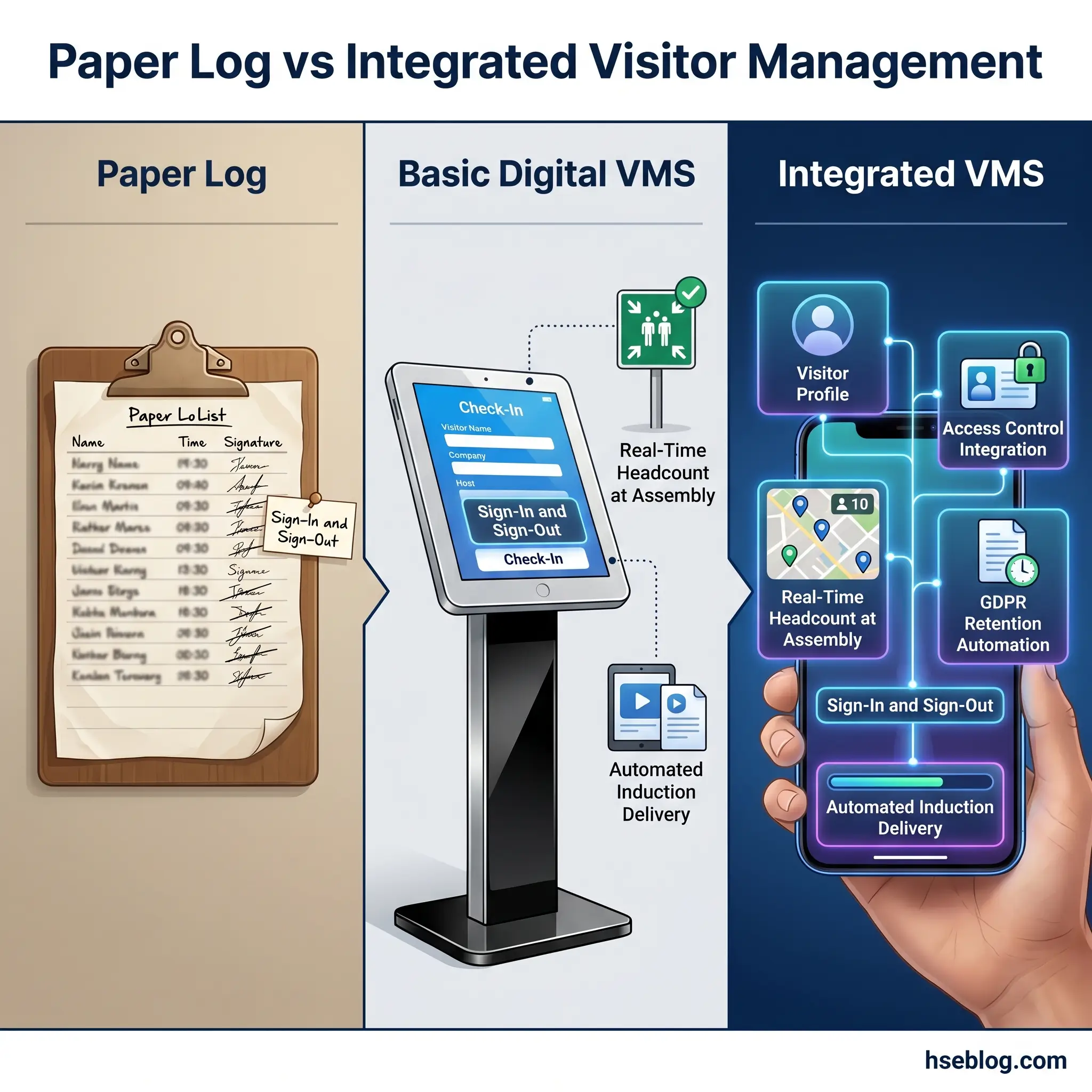
Visitor management systems — VMS — automate the operational grunt work of the visitor process. They print badges, send host notifications, capture digital sign-offs, and produce audit logs. What they do not do is convert a weak safety program into a strong one.
The visitor management system market was valued at $1.63 billion in 2023 and is projected to grow at 13.4% annually through 2030 (Grand View Research, cited in industry reporting, 2024) — a trajectory that reflects genuine HSE-relevant capability, not just convenience. The capabilities worth evaluating against safety objectives:
- Real-time occupancy tracking — accessible at the assembly point during evacuation, ideally on a mobile device the warden carries, so visitor accountability does not depend on retrieving a paper log
- Automated induction delivery — pre-arrival or at-arrival video or interactive briefing, with verifiable digital sign-off, ensuring the induction is actually delivered rather than skipped under time pressure
- Access control integration — badge or QR-code-driven door restrictions that enforce zone boundaries automatically, removing reliance on the visitor remembering where they are not allowed
- Watchlist and screening integration — for higher-security environments, integration with denial lists or background checks
- Audit-ready logs — sign-in, sign-out, induction completion, and acknowledgment all timestamped and exportable for inspectors or litigation discovery
- GDPR-compliant data handling — configurable retention, automated deletion, consent capture, and data subject access support
| Capability | Paper Log | Basic Digital VMS | Integrated VMS |
|---|---|---|---|
| Sign-in / sign-out | Yes (manual) | Yes | Yes |
| Real-time headcount at assembly | Difficult | Possible | Yes (mobile-accessible) |
| Automated induction delivery | No | Limited | Yes |
| Access control integration | No | No | Yes |
| GDPR retention automation | Manual | Partial | Yes |
| Multi-site reporting | No | Limited | Yes |
The caution on VMS is straightforward: implementing a digital system is not the same as having a visitor safety program. The technology handles logistics. The program — risk assessment, induction content design, escort discipline, drill testing, policy governance — is the responsibility of the HSE function. A VMS rolled out without that program in place often produces a polished sign-in experience that masks an unchanged underlying risk profile.
GDPR compliance is the secondary benefit of a configurable VMS. Visitor logs that auto-delete after a defined retention period (commonly 30 to 90 days for routine office visitors), capture explicit consent at the point of entry, and support data subject access requests are vastly easier to defend than spreadsheets and clipboards. The configuration matters: a VMS with retention set to “indefinite” carries the same GDPR exposure as a paper log kept forever in a cupboard.
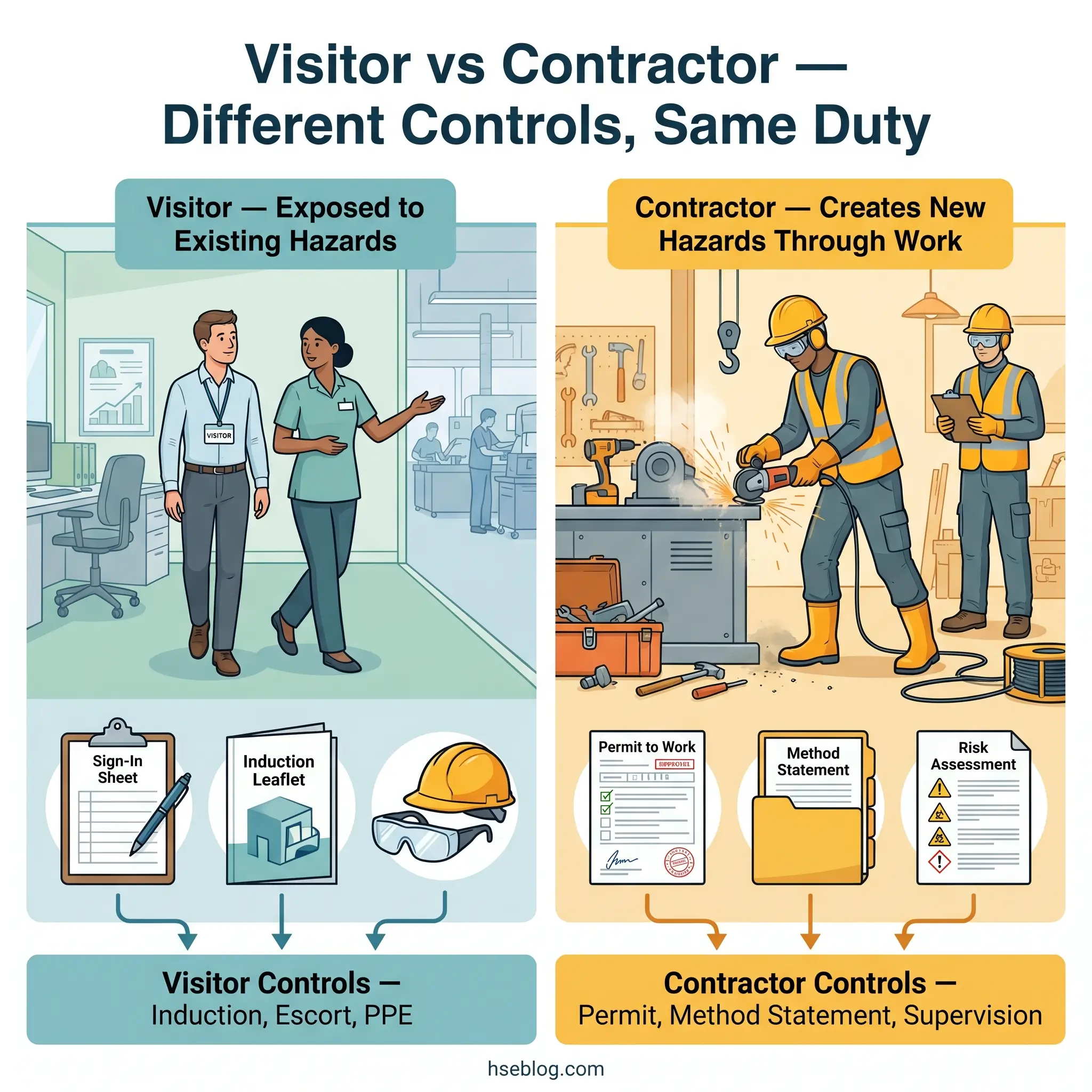
Contractor vs. Visitor: Understanding the Safety Management Distinction
Misclassification sits at the heart of one of the more preventable categories of multi-employer-workplace injury: the contractor who is given a visitor badge instead of full contractor induction. The administrative shortcut is small. The exposure consequence is large.
The distinction is functional, not cosmetic. A visitor is exposed to the workplace’s existing hazards. A contractor performs work — and creates new hazards through that work. The control mechanisms differ accordingly. Visitors are managed through induction, escort, and PPE. Contractors are managed through permit-to-work systems, method statements, competency verification, lock-out/tag-out integration, and ongoing supervision against the work plan.
| Dimension | Visitor | Contractor |
|---|---|---|
| Hazard relationship | Exposed to existing hazards | Creates additional hazards through work |
| Documentation | Sign-in, induction sign-off | Method statement, risk assessment, permit-to-work |
| Competency | Not required for safe presence | Required for the work being performed |
| Supervision | Host or escort | Site supervisor and competent person |
| Duration / scope | Single visit, defined area | Defined scope, possibly multi-day, work-specific area |
The grey areas are where misclassification happens. A vendor conducting a product demonstration — are they a visitor or a contractor? An auditor sampling work at heights — visitor or contractor? The defensible rule is to err on the side of the more protective classification. If the person’s activity could create a hazard, alter a system state, or require equipment beyond what a visitor would normally carry, they should be managed as a contractor regardless of how they are described in the diary entry.
The host employer’s duty does not transfer with classification. Under HSWA Section 3 in the UK and the General Duty Clause in the US, the host’s obligations to non-employees apply whether the person is classified as a visitor or a contractor — the difference is the control mechanism, not the existence of the duty.
Frequently Asked Questions
Conclusion
Visitor safety management resolves into a small number of decisions made well, rather than a sprawling policy made elaborate. Tier the visitors by destination and exposure, and scale controls accordingly. Connect sign-in to evacuation accountability so the log is operational, not administrative. Brief at sign-in or escort the unbriefed visitor every step. Configure data retention to match what GDPR or CCPA actually permits. Verify induction comprehension where the tier requires it. Walk the policy with an auditor’s eye annually rather than reading it from a desk.
The misconception that opens this article — that visitor management is a security or reception function — is the one most organizations grow out of after the first inspection finding or near-miss involving a non-employee. The cheaper path is to grow out of it earlier, by treating visitor safety as the HSE discipline that the regulatory record has always said it is. The legal duty is already in place under HSWA Section 3, OSHA’s General Duty Clause, and ISO 45001:2018 — and across 5,070 fatal work injuries recorded in the United States in 2024 (US Bureau of Labor Statistics, 2025), a meaningful share involved non-employees, even though no national statistics isolate them. The numbers exist, attached to people. The duty is the operational response.

